Are Employees Falling for Phish?
If you have employees clicking on links, or responding to BEC and zero-day attacks, it’s time to mitigate the risk and prevent a security breach.
 Learn how you can improve your response to sophisticated threats, with:
Learn how you can improve your response to sophisticated threats, with:
- Layering risk detection for sophisticated attacks and social engineering
- Applying layered controls, including Smart Banners, to educate employees
- Incorporating link rewriting and machine vision to destination websites
- Getting notifications when employees ignore warnings
Download the Whitepaper
"GreatHorn perfectly combines power and flexibility with the simplicity of an API solution."
— Director Of IT in the Services Industry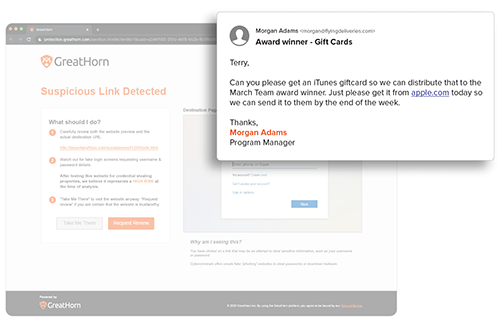
Suspicious URL Detection
URLs are analyzed using machine vision to detect any anomalous content on the destination. With GreatHorn’s Link Protection page, users are educated with a preview of the destination, the risk of credential harvesting, and steps they should take to minimize their risk.
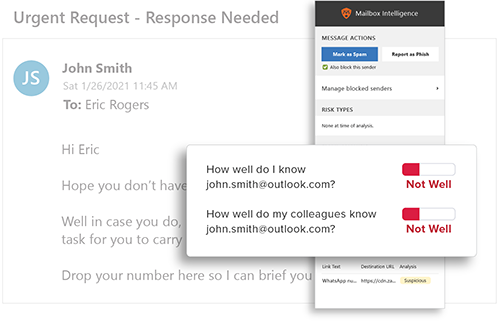
Behavioral Analytics
GreatHorn analyzes all communication patterns between senders and recipients using behavioral analytics within our AI and ML models, providing organizations with immediate detection and insight into anomalous emails.
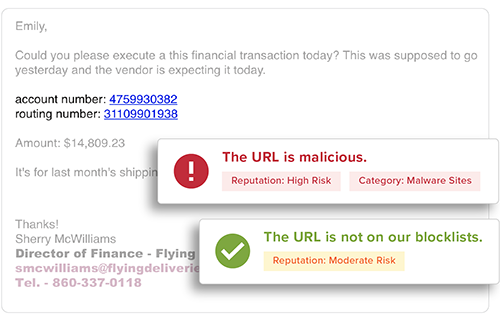
End User Education
Provide users with the context they need to help them make better decisions by applying automated and customized banners, Mailbox Intelligence, Suspicious Link pages, and more.