Analysis of User Typing Patterns Provides Critical User Authentication with Minimal Disruption
 WALTHAM, MA—February 24, 2020—GreatHorn, the leading cloud email security provider focused on managing risk from advanced email threats, today unveiled the first and only biometric solution that effectively identifies compromised accounts and blocks takeover attempts by validating users with their unique typing patterns.
WALTHAM, MA—February 24, 2020—GreatHorn, the leading cloud email security provider focused on managing risk from advanced email threats, today unveiled the first and only biometric solution that effectively identifies compromised accounts and blocks takeover attempts by validating users with their unique typing patterns.
The addition of Account Takeover Protection to the GreatHorn Email Security platform—which automatically combines data science, machine learning techniques, and technical analysis with human context—ensures that customers have the most comprehensive and powerful protection against the most sophisticated threats. By leveraging passwordless authentication to further enhance its capabilities, GreatHorn ensures that organizations can now benefit from first-factor authentication without adding friction to end-user email workflows.
The Rising Risk of Account Compromise
Today, compromised cloud accounts can be extremely difficult to identify, often surfacing only after the compromised account has been abused, resulting in potentially significant financial and reputation damage to the affected organization. While multi-factor authentication (MFA) can be an effective strategy for reducing account takeover, a recent Redmond Magazine article reported that less than 10 percent of Microsoft’s enterprise customers have deployed MFA. With the launch of Account Takeover Protection, GreatHorn has introduced a way to identify compromised accounts that is easy to implement, difficult to bypass, and minimally disruptive for users.
Account Takeover Protection
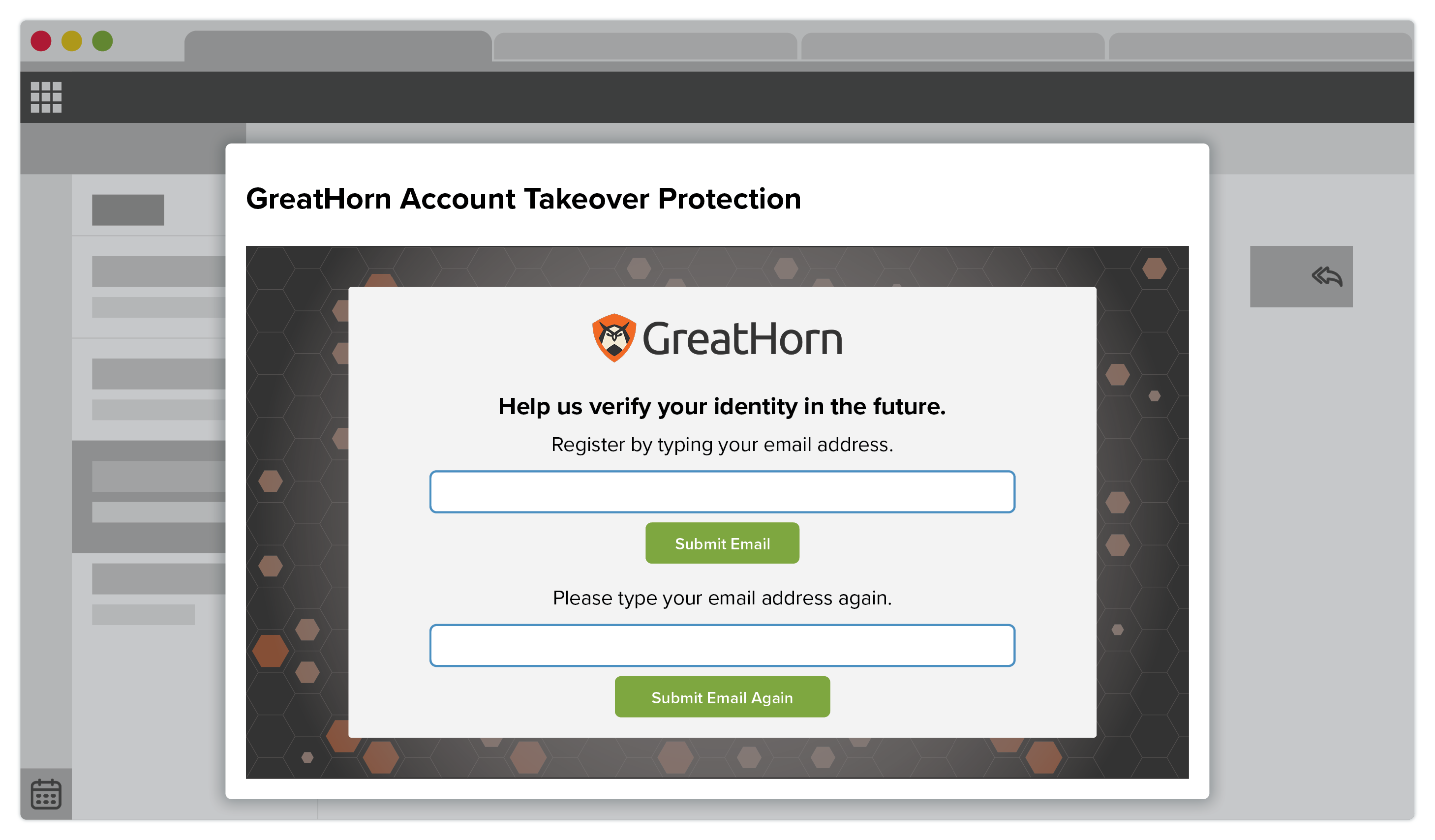
Built on top of GreatHorn Reporter, GreatHorn’s client-side plug-in, Account Takeover Protection uses machine learning techniques to capture a user’s unique typing pattern on both desktop and mobile devices. After initial authorization, GreatHorn will use a pre-determined trigger—e.g., frequency, time delay, or communication pattern anomalies—to reauthenticate the user. The tool does not capture keystrokes. It analyzes keystroke dynamics, such as speed, pressure, and timing between key press and release.
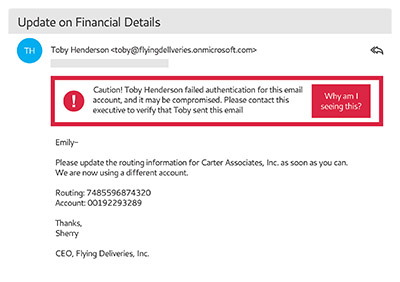
Administrators can configure actions based on authorization failures, such as inserting a warning banner to the recipient, removing the message upon send, alerting the security team, or simply logging the event for later analysis. Failed attempts populate into the GreatHorn dashboard, providing context for faster incident response.
The risk of account takeover is pervasive across all industry verticals. With increasing frequency, malicious actors are using social engineering, phishing, and other technical methods to circumvent multi-factor authentication in order to obtain the one-time passcode and access protected accounts. The takeover of just a single business account can have a far-reaching impact. At best, it reveals private company communication and provides access to confidential documents in Google Drive or SharePoint. But the compromised account can also be used to release a barrage of impersonation attacks that lead to substantial financial loss. Or worse, it can be used to access business-critical systems in order to wreak havoc on an enterprise.
“Most email solutions rely on binary or perimeter-based analysis to prevent email attacks, but these methods fail to identify when a legitimate account has been compromised,” said Kevin O’Brien, co-founder and CEO, GreatHorn. “Our Account Takeover solution uses proprietary, best-in-class keystroke analysis to match typing patterns as a unique identifier. Your typing pattern is unique to you and extremely difficult to replicate, making it highly accurate and nearly impossible to circumvent. And because the action of typing is a part of a user’s everyday workflow, it allows for periodic validation with minimal disruption.”
About GreatHorn
Global 2000 companies use GreatHorn to reduce the inherent and pervasive risk associated with the everyday use of email. GreatHorn’s multi-layered approach to email security automatically combines data science, machine learning techniques, and technical analysis with human context to protect organizations before, during, and after a phishing attack.
By treating email security as a risk management function, customers can not only detect and remove more attacks but also warn users in real time of potential threats and provide response teams with the tools to limit exposure and minimize risk. As a result, GreatHorn Email Security safeguards cloud email from advanced threats such as business email compromise, impersonations, credential theft, account takeover, and other phishing attacks.