Integrated Approach to Email Security
Get Even More Visibility Across Your Entire Email Security Stack
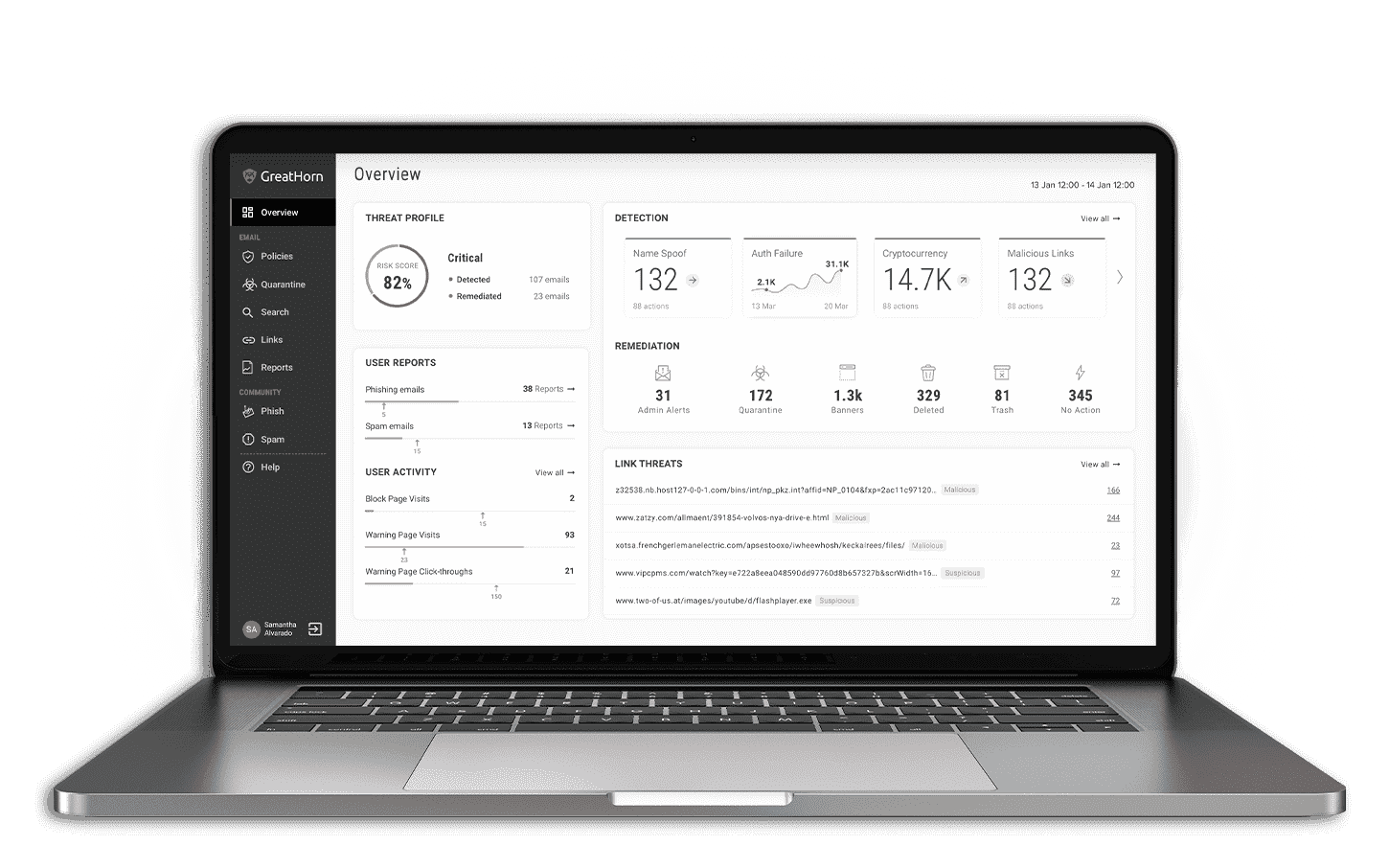
GreatHorn offers an exhaustive risk mitigation platform featuring an Integration Layer, extending capabilities to improve detection, incident response and reporting. This 360-degree insight allows organizations to drastically reduce both Mean-Time-to-Detect (MTTD) threats requiring further analysis and response and Mean-Time-to-Respond (MTTR) to ultimately remediate risks to an organization.
Pre-built integrations include:
Security Awareness Training
SOAR
DMARC
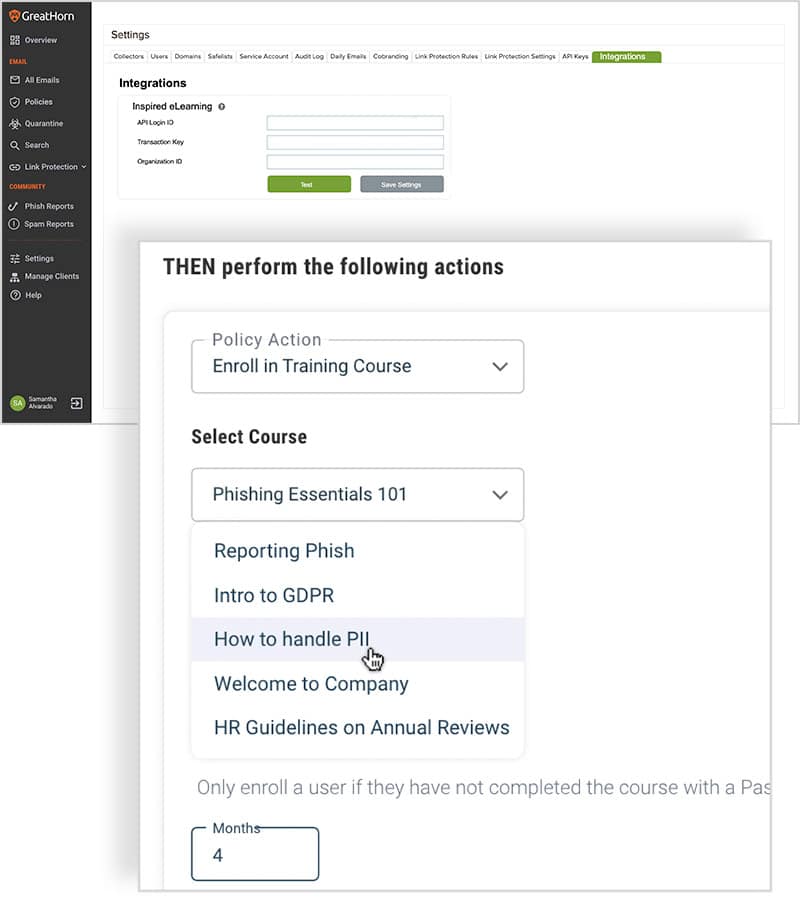
Security Awareness Training
The integration between email security and security awareness training refines risk profiles of end users and customizes policy actions to better protect organizations from threats. GreatHorn’s bidirectional, pre-built API integration with Inspired eLearning provides organizations with the facts organizations need to better detect and remediate risk.
GreatHorn + Inspired eLearning, the leading provider of cybersecurity and corporate compliance specializing in producing some of the most effective and realistic phishing simulation tools in existence.
Key Benefits:
- Improved end user risk profiling and scoring
- Culture shift to prioritize security and institute proactive behavioral practices
- Empowering employees to understand today’s risks so they can identify threats more effectively
- Expanded behavioral modeling for improved end user risk profiling and scoring
- Dynamically deploy a response that maps to a user risk based on past training performance
- Custom policy actions and enrollment between platforms
SOAR: Automate Your Response to Phishing
The integration between email security and security orchestration, automation and response (SOAR) technologies allows SecOps teams to orchestrate and remediate threats quickly using prebuilt or customized playbooks.
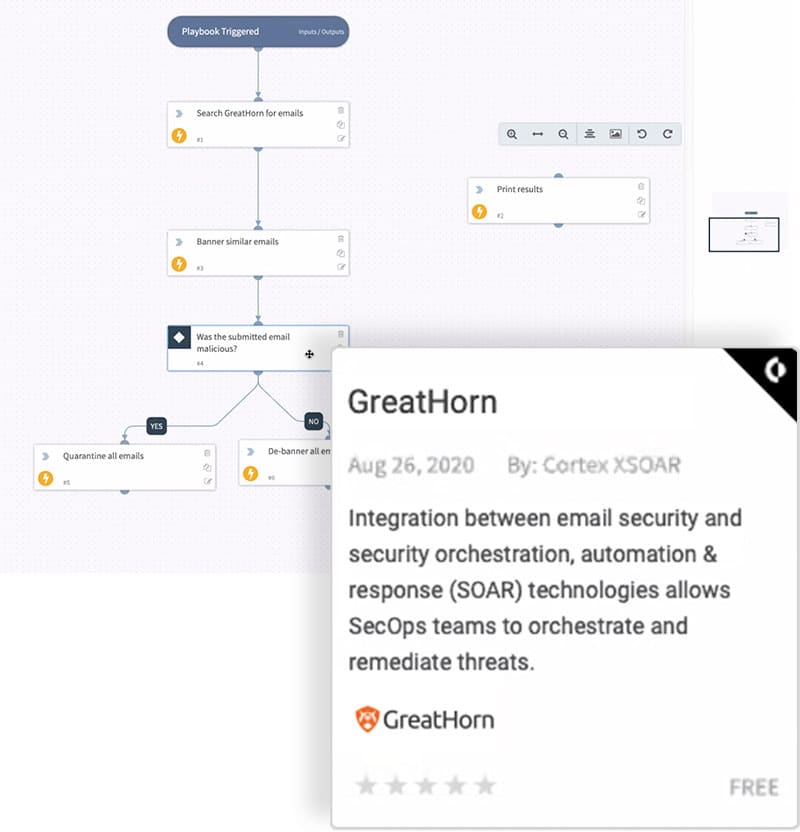
GreatHorn / Cortex™ XSOAR
GreatHorn + Cortex™ XSOAR, the industry’s only extended security orchestration, automation and response platform with native threat intelligence management.
Key Benefits:
- Ingest data from GreatHorn into proven playbook-drive automation to accelerate incident response
- Improve time to detect and investigate advanced threats
- Influence change risk types within GreatHorn to remediate actions, including message release, quarantine using “similar characteristics”, etc.
- Increase and/or automate response to employee requests to review/release messages from quarantine
- Comprehensive customization available to build policy actions between platforms
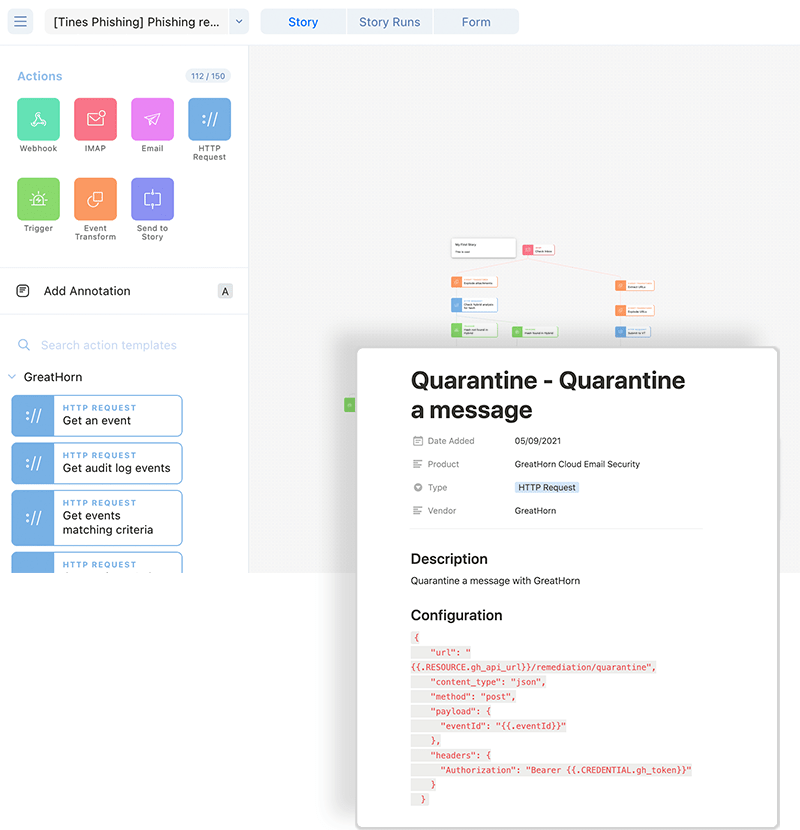
GreatHorn / Tines
GreatHorn’s bidirectional, pre-built API integration with Tines, provides IT security pros with the ability to extend the automation of repetitive processes into email security with prebuilt and customized templates from the Tines public template repository.
GreatHorn + Tines, makes it easy to offload monotonous workflows, giving you back time to increase your impact.
Key Benefits:
- Ingest data from GreatHorn into proven template-driven automation to accelerate incident response
- Improve time to detect and investigate advanced threats
- Automate the actions associated with quarantine, including auto-delete, auto-quarantine and release
- Create workflows to improve remediation actions, including applying smart banners, deletion, move to trash and much more
- Easily integrate GreatHorn with dozens of other security tools from threat intelligence, endpoint and network
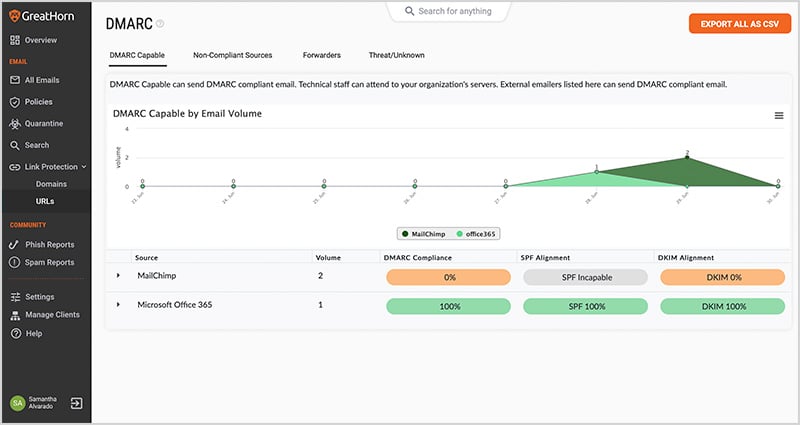
DMARC
By implementing DMARC protocol, in combination with the GreatHorn email security platform, organizations extend their email security to further protect their domain(s) from unauthorized use to combat phishing, spoofing, CEO fraud and business email compromise.
GreatHorn + dmarcian, the leading provider of DMARC that allows domain owners to secure their email domain.
Key Benefits:
- Eliminate unauthorized use of your domains to protect against spam, fraud and phishing
- Gain complete visibility to know “who” and “what” is sending email on your domains, including shadow IT
- Allow others to identify that your email is really coming from your organization
- Custom policy actions between platforms
![[eBook] Things to Consider: Microsoft 365 + GreatHorn](https://www.greathorn.com/wp-content/uploads/2023/05/eBook-Microsoft-365-GreatHorn.png)
![[eBook] Things to Consider: Google Workspace + GreatHorn](https://www.greathorn.com/wp-content/uploads/2023/05/eBook-Google-WorkspaceGreatHorn.png)
![[Whitepaper] Measuring the Value of Email Security Solutions](https://www.greathorn.com/wp-content/uploads/2023/05/Whitepaper-Measuring-the-Value-of-Email-Security-Solutions.png)
![[Report] 2023 State of Email Security: Key Trends and Insights](https://www.greathorn.com/wp-content/uploads/2023/03/Report-2023-State-of-Email-Security.png)