User Education In-The-Moment of Risk
Warn Employees of Risk When it Matters Most
Email threats don’t follow simulated patterns – and neither do employees. By going beyond interactive modules and simulations, you can help employees make safe decisions when faced with email threats, from phishing attacks and business email compromise to insider threats.
With GreatHorn’s easy-to-understand, digestible warnings, your employees can contribute to your organization’s security posture rather than detract from it with the right context at the right time.
Context-Specific
Get the information users need to take back control of their inbox.
Customizable
Add specific instructions based on the type of threat and your risk types.
User Control
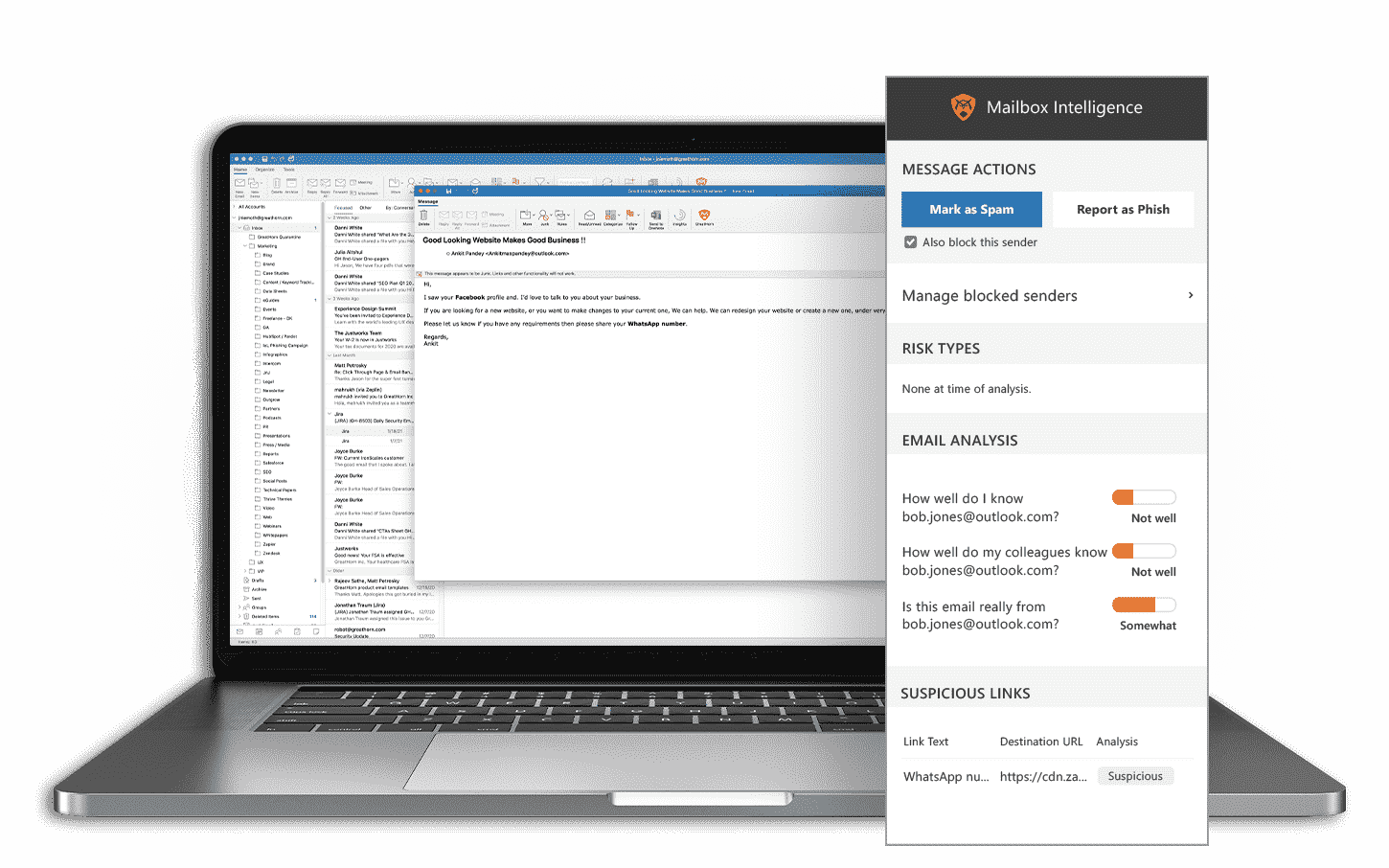
Empower users to report phish and create custom block lists.
Get Your FREE Email Threat Assessment
Learn what advanced threats are currently getting through your existing email security and into your end users’ mailboxes.
Help End-Users Make Better Decisions
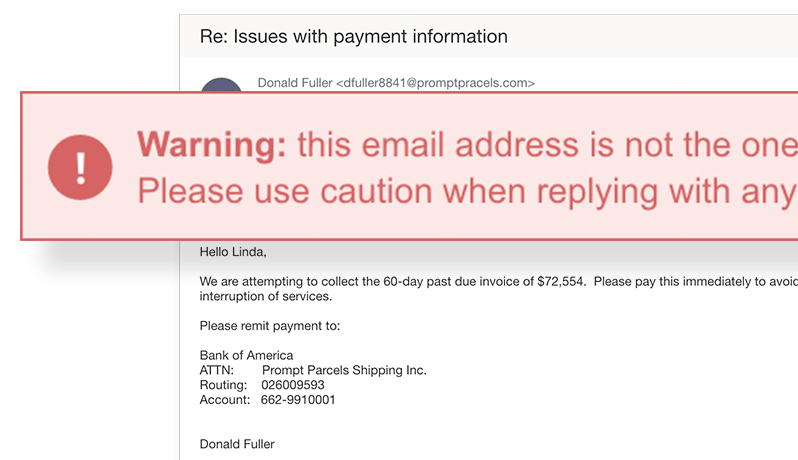
Provide your end-users with insights into suspicious email to help them make better decisions.
GreatHorn’s fully customizable smart banners can contain specific instructions and context relevant to an individual email to warn employees of a specific threat. Branding options help employees know when the alert is real.
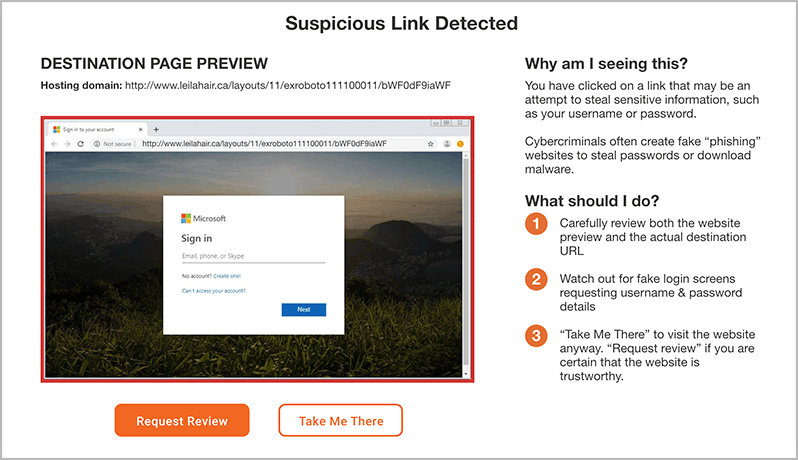
Preview Suspicious Links and Block Credential Theft Sites
By analyzing the email, domain, context, and hundreds of other factors, GreatHorn identifies and blocks known malicious sites and can provide previews of links deemed suspicious.
GreatHorn’s suspicious link preview also uses advanced computer vision to determine if a destination site is a credential theft site, blocking employees from accessing it.
Identify and Remove all Instances of an Emerging Attack
GreatHorn’s client-side plug-in offers “Report-as-Phish” capabilities to contribute to your security posture. Since these reports are integrated directly into GreatHorn Email Security, response teams can easily determine if the threat is real, and quickly identify and remove other instances of an emerging attack.
The plug-in also provides employees with stoplight-level analysis of a given email’s risk level in easy-to-understand terms.

Company Closes Email Security Gap
“With GreatHorn, we get a multi-layered approach to email security – not just prevention of known threats and targeted phishing attacks, but also in-the-moment user awareness training and incredibly effective remediation tools. As a result, my security team spends less time on email threat management and more time on other critical security areas.”
![[eBook] Things to Consider: Microsoft 365 + GreatHorn](https://www.greathorn.com/wp-content/uploads/2023/05/eBook-Microsoft-365-GreatHorn.png)
![[eBook] Things to Consider: Google Workspace + GreatHorn](https://www.greathorn.com/wp-content/uploads/2023/05/eBook-Google-WorkspaceGreatHorn.png)
![[Whitepaper] Measuring the Value of Email Security Solutions](https://www.greathorn.com/wp-content/uploads/2023/05/Whitepaper-Measuring-the-Value-of-Email-Security-Solutions.png)
![[Report] 2023 State of Email Security: Key Trends and Insights](https://www.greathorn.com/wp-content/uploads/2023/03/Report-2023-State-of-Email-Security.png)