Mailbox Intelligence
Arm Email Security’s Best Line of Defense – Your People
When it comes to securing your organization, employee behaviors can often be a source of both unnecessary risk and concern. Yet when it comes to protecting against business email compromise, impersonations, brand lookalikes, and advanced spoofing attacks, those very employees—if given the right context and information—can be your best, last line of defense. GreatHorn Mailbox Intelligence empowers end users to take action from the front lines, further reducing your organizations’ susceptibility to today’s advanced email attacks.
Meaningful Context
Give end users the facts they need to make better decisions at the moment they open and interact with emails.
.
Empower End-Users
Give users the ability to become part of the solution by reducing the presence of Phish and SPAM in their inboxes.
Improve Detection & Response
Receive instant notification of reported Phish to more effectively and efficiently remediate threats across all your users’ inboxes.
Get Your FREE Email Threat Assessment
Learn what advanced threats are currently getting through your existing email security and into your end users’ mailboxes.
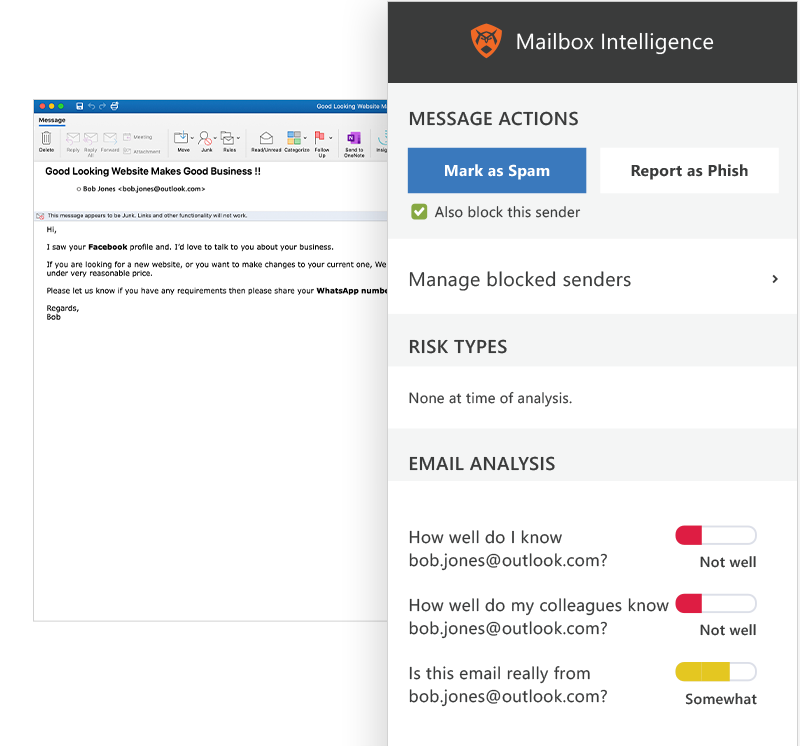
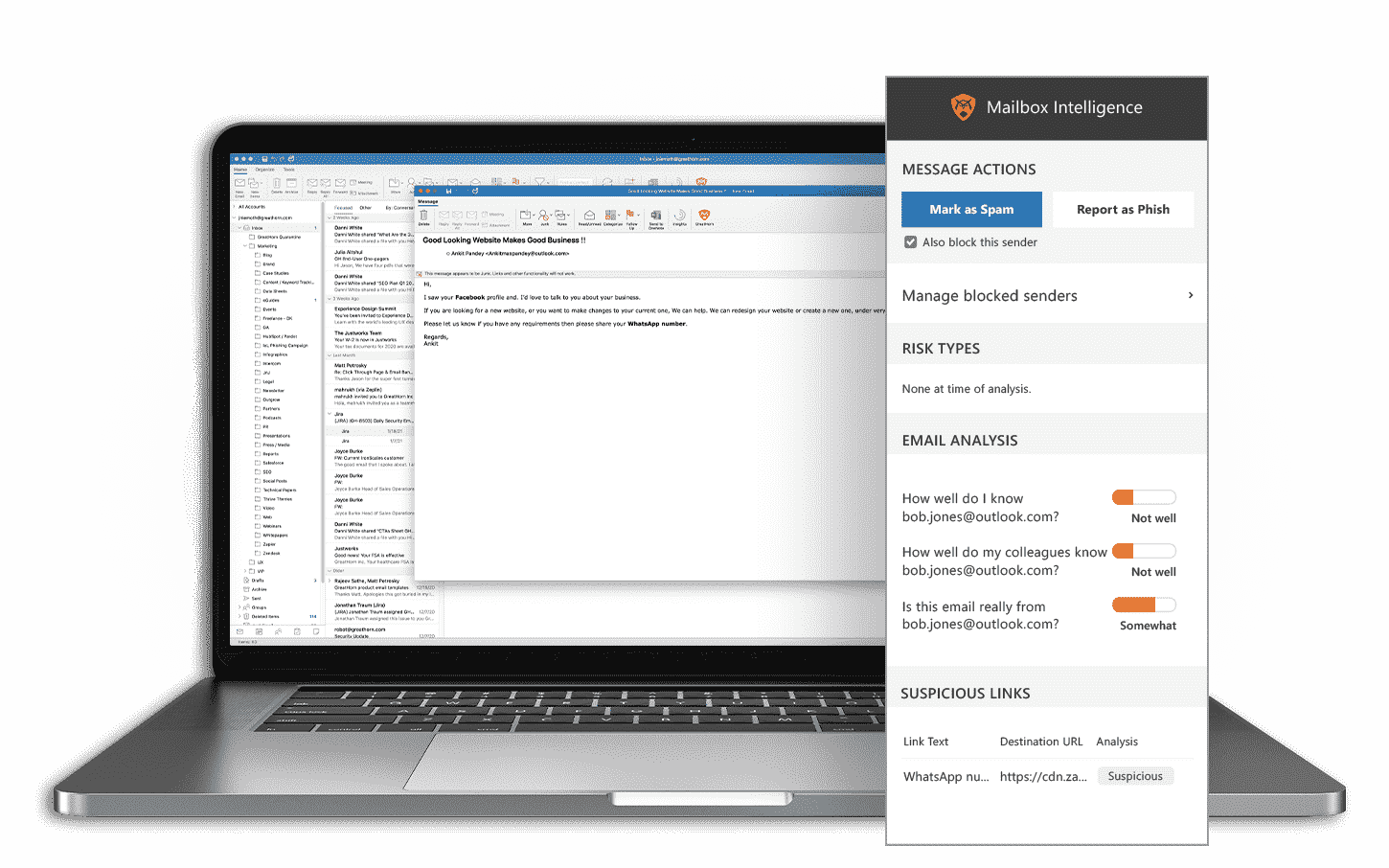
Visual Facts At the Moment of Risk
Deliver digestible insight to users as they interact with emails. Stop-light visibility into any sender and domain trustworthiness, relationship strength, and suspicious link warnings, help users evaluate the risk within every email.
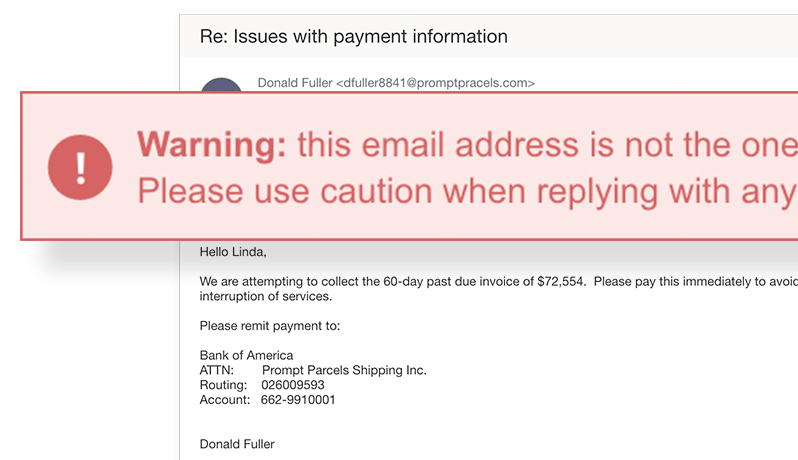
In-Context Notifications Driving Informed Behavior
1 in 25 people will click on any given phishing attack. With GreatHorn Mailbox Intelligence, additional smart bannering of emails provides customized notifications with specific warning messages, training your employees to recognize real-world phishing attempts and suspicious emails–reducing your risk posture.
GreatHorn Mailbox Intelligence complements existing security awareness training by providing real-time insights when they needed it most – at the moment of risk.
Proactive Risk Reduction in Users’ Hands
Help your end users make better decisions when interacting with email, while giving them the tools to make a meaningful contribution to the organization’s security posture with “Report as Phish” capabilities.
Employees can easily report phish, remove spam, and even create personalized block lists to reduce unwanted mail.
Layered Protection with Suspicious Link Previews
GreatHorn goes beyond blocking traditional “known bad” URLs, identifying suspicious links being received by end users within your organization. Using advanced computer vision to determine if a destination site is potentially malicious, GreatHorn assesses suspicious URLs providing a link preview to warn your end users of potential risks. And, because suspicious links could become weaponized at any moment, we provide your organization with on-click analysis to further protection your organization.
![[eBook] Things to Consider: Microsoft 365 + GreatHorn](https://www.greathorn.com/wp-content/uploads/2023/05/eBook-Microsoft-365-GreatHorn.png)
![[eBook] Things to Consider: Google Workspace + GreatHorn](https://www.greathorn.com/wp-content/uploads/2023/05/eBook-Google-WorkspaceGreatHorn.png)
![[Whitepaper] Measuring the Value of Email Security Solutions](https://www.greathorn.com/wp-content/uploads/2023/05/Whitepaper-Measuring-the-Value-of-Email-Security-Solutions.png)
![[Report] 2023 State of Email Security: Key Trends and Insights](https://www.greathorn.com/wp-content/uploads/2023/03/Report-2023-State-of-Email-Security.png)