They’re the worst fear of IT professionals. Literally.
According to a recent survey, 52% of cybersecurity pros are most concerned with malicious payloads being delivered via email, and 47% are most concerned with malicious payloads being delivered by a hyperlink within an email. There’s a good reason for their concern: attackers use them as an entry point to do further damage. Once a user downloads a malicious payload onto their machine, the attacker can move laterally to continue their attack.
Attackers frequently use spear phishing techniques to attempt to get users to download a malicious payload, specifically targeting individual users with fraudulent emails. As Gartner Research VP Peter Firstbrook noted in a recent analysis (subscription required), the SolarWinds attack, which used malicious payloads at multiple stages, originated with a spear phishing attack.
“SolarWinds’ code was compromised in the development process, which has significant implications for the development community,” he wrote. “Developers are targets of advanced spear phishing attacks that can easily lead to compromise on Linux machines, which are excluded from EDR [endpoint detection and response] requirements.”
The SolarWinds attack was the result of continuous efforts by attackers to deploy new malware. Hackers are continually trying new methods: zero-day attacks and permutations of existing malicious files. In this environment, a “known bad” list of malware isn’t enough. If this magic list were out there, Google, Microsoft and every other large security vendor would have acquired it. Unfortunately, it doesn’t exist. Over and above “known bad,” a layered approach to email security is required.
Zero-Day Attack
In February 2021, the GreatHorn Threat Intelligence Team identified a new malicious payload, which cybercriminals were attempting to deploy through spear phishing attacks. Between February 1 and February 15, 2021, the delivery of this malicious payload via email increased 40%, and subsequently increased 125% between February 15 and March 7, 2021. The most significant target of these spear phishing emails were individuals residing in the finance department.
Since GreatHorn is an API cloud email security vendor, emails have been inspected and managed by the native email platform provider (Microsoft 365 and Google Workspace) prior to being inspected by the GreatHorn platform. Because it takes time to detect a new piece of malware and place it on the “known bad” list, these attacks were getting through those native email provider’s defenses and landing in users’ inboxes. Here’s a quick review of what we found.
Troj/Phish-HUP was first seen in February 2021. Organizations attacked with email phishing campaigns that included this malicious payload would not have had email security coverage to strip the email of the attachment, based on the contents of the file alone. It’s used in targeted attacks on Microsoft Windows operating systems (Details)
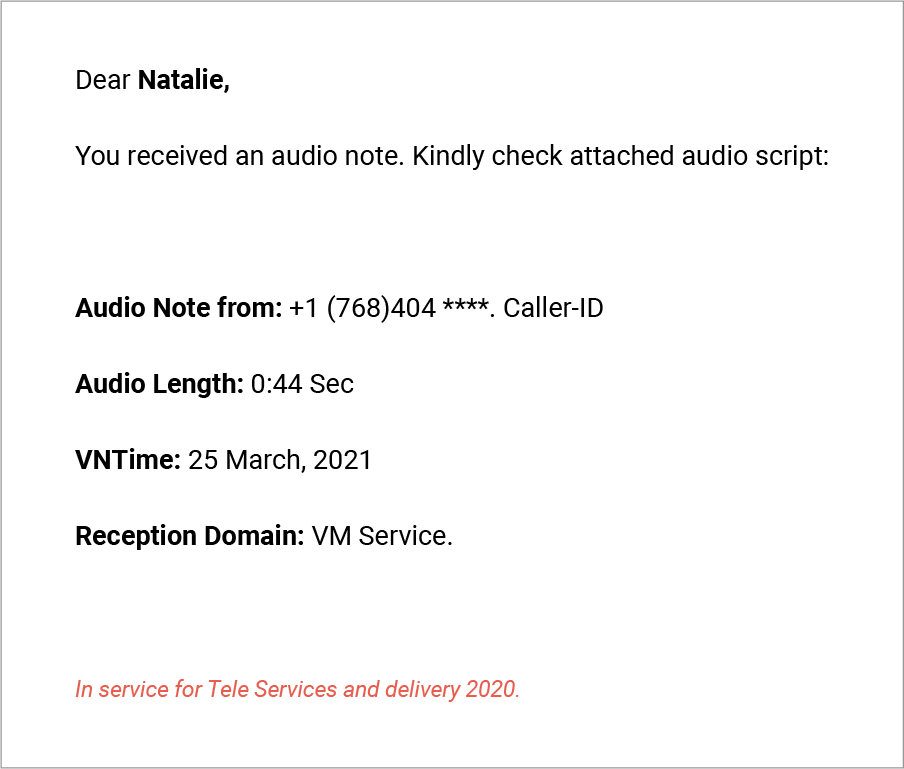
The Troj/Phish-HUP malicious payload is a “Trojan horse,” a malicious file designed to look normal or legitimate. Attackers used spear phishing emails, disguised as normal communications in which users would expect to download a file. Here is an example of one such email:
- Subject:
- [“New (44 seconds) message from (768)404 **** on February 17, 2021, 11:56:18 AM”]
- [“_(5973440922) has left you a message 35 second(s) long”]
- Other permutations of similar
- Display Name:
- “COMPANY NAME system¬Æ”
- “COMPANY NAME caller”
- Body of Email:

Known-Bad Malicious Payloads
Even malicious payloads that are known bad and on lists can be missed within native email platforms and legacy email security systems. For example, in February 2021, the GreatHorn Threat Intelligence Team identified widespread attacks containing malicious files that were already on known-bad lists. Again, these attacks found ways to slip by defenses put in place by native email platforms.
A Layered Approach
With attackers continuing to develop new attacks using malicious payloads, organizations with sensitive data and systems to protect cannot rely on native email platform security alone. A layered approach is needed – sometimes even just to protect against known-bad files.
Download the Malicious Payloads and Ransomware eBook to get the facts on the latest facts and trends.
Find out more about how GreatHorn goes beyond known bad to flag suspicious emails based on data from users’ history and protect your organization from malicious payload attacks.