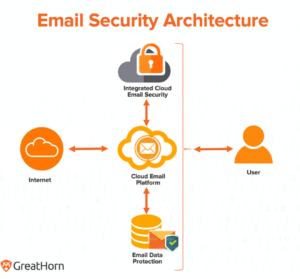
The shift from on-premise email platforms to cloud email platforms has taken shape, with the majority (70%) of organizations. Microsoft 365 and Google Workspace remain the predominant email platforms for organizations. However, a significant change has occurred in the past year. With an estimated 40% of ransomware attacks that start through email, and BEC and account takeover threats continuing to rise, organizations are reevaluating the capabilities and effectiveness of their current solutions compared to new products. There is now a new focus on the email security stack and what the recommended framework looks like to protect against phishing attacks most effectively.
Cloud Email Platform Controls
Many organizations are beginning to realize the benefits of the built-in protection available at the platform level (i.e. Microsoft O365 and Google Workspace). As Gartner notes in the 2021 Market Guide to Email Security, “by 2023, at least 40% of all organizations will use built-in protection capabilities from cloud email providers rather than a secure email gateway (SEG)…” This significant shift is primarily due to the enhanced functionality now available at the platform level. So instead of duplicating functionality and increasing budgets, organizations are now understanding what capabilities are available at the platform level and finding alternative email security solutions for enhanced functionality.
What to Use in the Native, Cloud Email Platform Controls:
- Blocking emails from known bad senders
- Scanning attachments with AV
- Blocking emails with known bad URLs
- Content analysis to identify SPAM
API-Based Email Security Controls
Gartner has now updated email security solutions that use APIs to examine emails, calling them Integrated Cloud Email Solutions (ICES). These solutions, “use sophisticated anomaly detection techniques like natural language understanding (NLU), natural language processing (NLP) and image recognition. The direct integration makes these solutions easy to evaluate and prove value, and because they are behind any existing controls, the value can be seen quickly.” And, when using advanced email security solutions, they have much faster deployment and time to value, as they use API access to the cloud email provider to analyze email content without the need to change the Mail Exchange (MX) record.
As stated by Gartner, “integrated solutions go beyond simply blocking known bad content and provide in-line prompts to users that can help reinforce security awareness training, as well as providing detection of compromised internal accounts. Initially, these solutions are deployed as a supplement to existing gateway solutions, but increasingly the combination of the cloud email providers’ native capabilities and an ICES is replacing the traditional SEG.” When assessing your email security framework, using native platform controls with the additional layers of sophisticated threat protection controls in ICES solutions, organizations can most effectively address the risks represented in email.
What to Use in ICES, with Layered Native, Cloud Email Platform Controls:
- BEC and Account Takeover Attacks using NLU, NLP, social graph analysis and image recognition
- Context-aware banners to warn users
- Phish Reporting
- MSOAR capabilities to assist in automatic reclassification of emails and removal from inboxes
Evaluation Criteria for ICES Email Security Vendors
When evaluating your current email security framework and comparing to your desired state, the following considerations should be analyzed:
- ML- and AI-based technology to address BEC attacks and analyze conversation history
- Computer vision to analyze suspicious links
- Mechanism to report phish
- Reported emails by the user get processed by MSOAR capabilities to automatically remove from inboxes
- User education controls to reinforce training, including context-aware banners and/or in-line prompts
- Analyze emails prior to delivery to the end user
- Integration of email events into XDR or SIEM/SOAR
- Simple evaluation
- Managed services to support team
For more information on how to effectively address email-based risk using a layered, defense-in-depth approach –
Try GreatHorn for 30 Days, Risk Free!

