In phishing, the goal is to steal individuals’ bank, credit card, and personal details so they can be sold off on the black market. Easy and fast money is usually the goal for the cybercriminal.
If you ask most people, they’d likely tell you they could identify a phish when reading through their emails. Of course, the Nigerian prince isn’t going to give you millions if you deposit $100,000 into his bank account – delete that email. But what about the more sophisticated attacks we’re seeing today?
Phishers often create fake email addresses that look like they were sent from legitimate ones. Although the sender’s name may be visible, the email address is often hidden. In an Amazon phishing email, for example, the visible alias might be “Amazon Support,” but the hidden email address is “[email protected].” The goal is for the recipient to trust the sender’s name is legitimate and not double-check the email address. With many users checking email on their mobile device, this can be an easy way to trick someone with their guard down.
To complicate things, our attention spans are becoming shorter as the demand for our attention becomes greater. And with improvements to technology and overflowing inboxes, it is becoming increasingly difficult for users to identify a phish. Here are a few examples below – let’s see if you can catch a phish! And, if you want to test your skills, sign up to participate in “To Catch A Phish,” where you’ll get 10 real world emails sent to you (minus the without any malicious links or files).
Examine the example below:
Original Url: hxxps://firebasestorage.googleapis.com/v0/a/……………..
Brand Target: Facebook
Display name: Faceb00k
Subject Line: ACC0UNT SUSPENSI0N NOTICE.
via SendGrid CIDR: 149.72.0.0/16
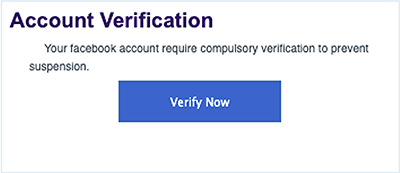
Did you see the double zeros appearing as an ‘o’ in the display name and subject line?
Grammatical errors are a sure-fire way to detect a phishing email. Phishing emails also tend to contain language that attempts to make users act quickly. If you receive an email like this from an organization about your account or account information you should always proceed with caution.
Example #2: DocuSign Phishing Email
Examine the example below:
Original Url: hxxps://firebasestorage.googleapis.com/v0/a/docu……………….
Brand Target: DocuSign
Display name: Docusign Via Docusign
Subject Line: Completed: Please DocuSign
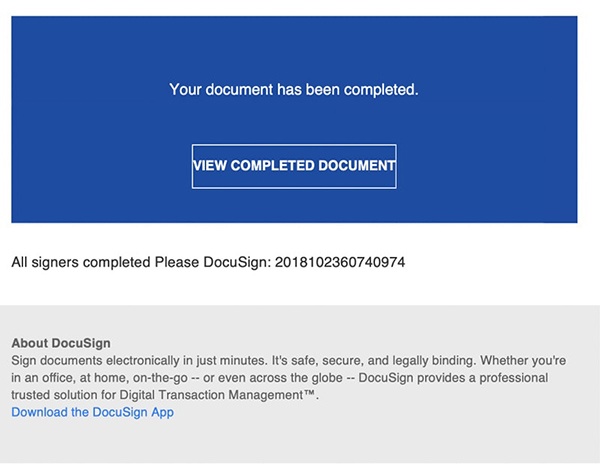
Do you normally authorize contracts for your organization? Are you expecting to receive an agreement via DocuSign? Did you just sign an agreement and are expecting a return signature? A good rule of thumb is that if it seems out of place, it probably is. Always be cautious of links in emails. If you don’t have an email security solution the protects you from suspicious or malicious links, hover over links in email messages to verify a link’s actual destination – even if the link is coming from a trusted source. You can also type in website addresses rather than using links from unsolicited emails.
Example #3: DHL Phishing Email
Examine the example below:
Original Url: https://firebasestorage.googleapis.com/v0/a/my/…………………
Brand Target: DHL
Display name: DHL
Subject Line: Delivery Failed
via SendGrid CIDR: 168.245.0.0/17
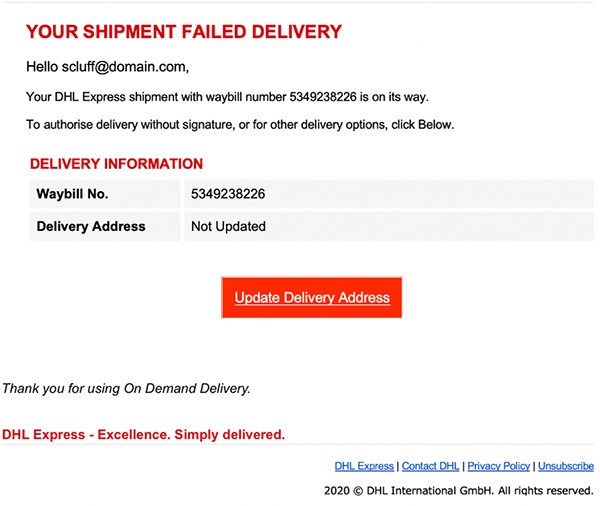
Are you expecting a package? Have you placed an order recently that’s being shipped via DHL?
While not technically misspelled, the use of ‘authorise’ in the above email triggers the spellcheck because it’s not commonly used as a spelling variant of the word ‘authorize’ in America. This could be a red flag that the email is a phish. If you see spelling or grammatical errors in the subject line or body copy you should proceed with caution.
If you fall victim to a phishing email at your organization, follow the policy that is prescribed by your employer and notify your email administrator. It would also not be a bad idea to turn off your computer to help prevent the spread of any infection into the network. If your employer doesn’t have a policy around phishing, read our blog titled “What to Do If You Click On a Phishing Link.”
If you’re looking to see how well you fare against phishing attacks, sign up “To Catch a Phish” and receive 10 phishing simulation emails to understand how easily you can be deceived by cybercriminals!




