In GreatHorn’s blog series, “Phishing Emails, Explained,” we take a closer look at real-world phishing emails and the tactics cybercriminals use to lure victims into interacting.
One of the more common email phishing attacks is the “voicemail message” or “missed call” message scam. Just like other types of phishing, voicemail notification email messages prey on human curiosity – I wonder who called me and why? Many of these phishing attempts fail because of the not-so-legitimate appearance of the messages. However, there are a few targeted attacks that we’ve seen recently that may trick distracted, overworked recipients.
Before we look at some examples, let’s clarify that this “new voicemail message” scam should not be confused with vishing, which is something totally different.
What is vishing?
The voicemail phishing attempt – a classic. Leading to annual global losses in the billions, these voice scams rely heavily on social engineering and manipulation to get victims to give away information.
With vishing, scammers typically pretend to be from a trusted/official source, such as a bank or government organization. Many scams may originate outside the target’s country. As such, many scammers will use voice-to-text technology and recorded messages to mask their identity. Those based in the recipient’s own country may also use a real human on the other end of the line for more targeted scams.
Most vishing attempts try to convince the victim to give up PIN numbers, Social Security numbers, credit card security codes, passwords, or other personal details. In some cases, the vishing scammer will attempt to gain access to personal accounts or bank accounts in order to steal information or money.
Similarly to our “new voicemail” email phishing example, information gathered from a successful vishing expedition will be used for some type of identity fraud, or to steal money directly from an account.
The “new voicemail message” phishing attempt
Since phishing relies on the fact that recipients are busy at work and not necessarily scrutinizing emails before opening them, these types of email scams are often successful.
In this example, the “new voicemail message” email looks legitimate because of the images and text in the body of the email. The message displays an “official” Microsoft software logo along with text stating the message comes from a “trusted source.”
The scammers take the scam one step further by adding additional content in the email. Some versions of the email scam have a portion of a voicemail transcribed in the email. “Please contact me ASAP about…” is an example. And once you click the link, it will download malware onto your computer or redirect you to a fake credentials form to fill out.
EXAMPLE 1: Voice Message Notification from Unified Messaging System
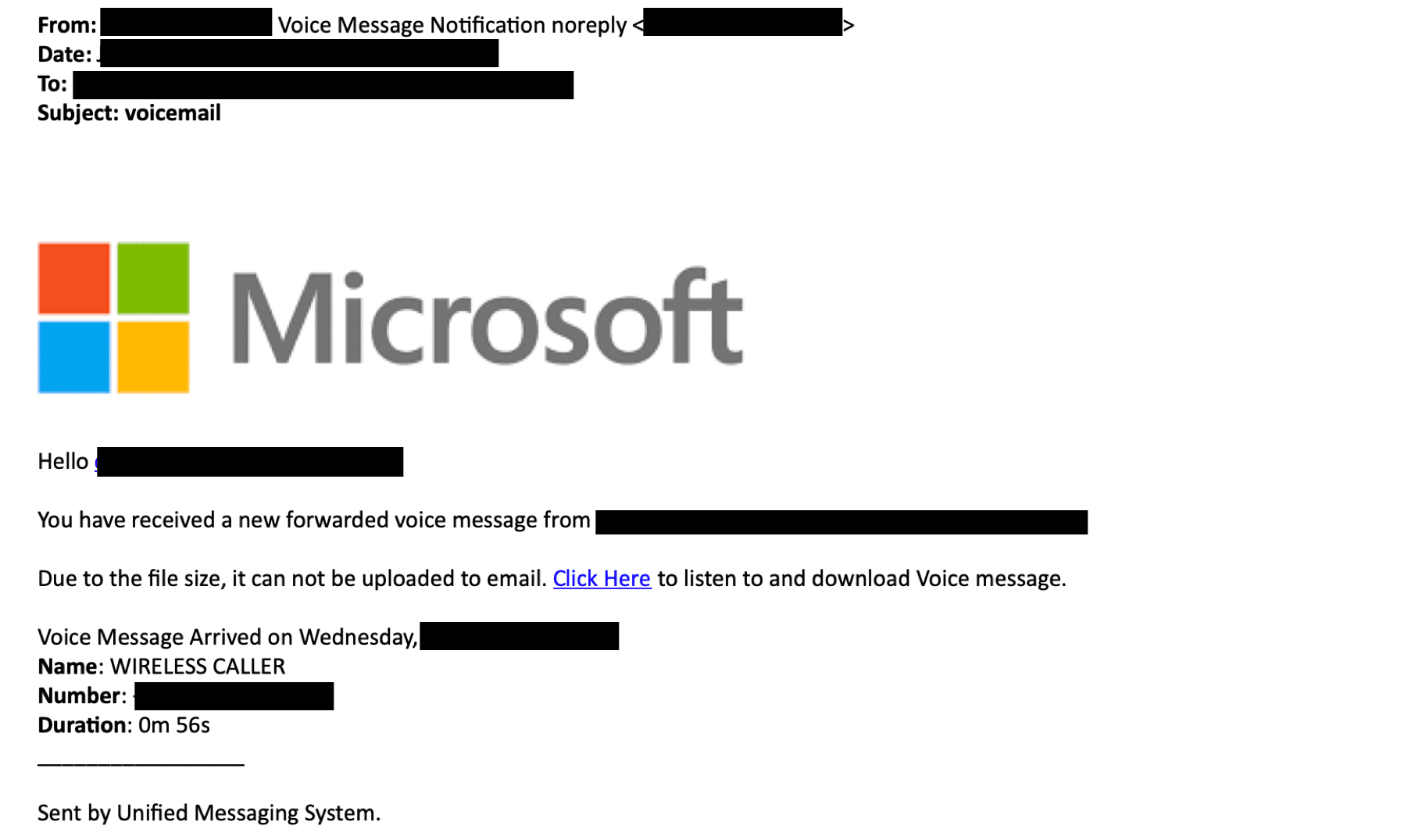
The below example shows a phishing email that claims to come from Microsoft’s Unified Messaging System.
The “From” field:
“Voice Message Notification noreply”
After double checking the sender domain of this message, it shows that the email does not come from a Microsoft domain.
The subject:
voicemail
The body:
“Hello, You have received a new forwarded voice message from (x) on November 23, 2019 1:50 PM.
Due to the file size, it cannot be uploaded to email.”
The call to action:
“Click here to listen and download voice message.”
The goal:
To convince the recipient that he/she has a new voicemail recording that is too large to send directly via email. To trick the recipient to click on the CTA in order to steal the recipient’s credentials.
EXAMPLE 2: “New Voicemail Message in Mailbox”/h3>
The below example shows a phishing email that claims to come from Microsoft “Office 365 Message Centre.”
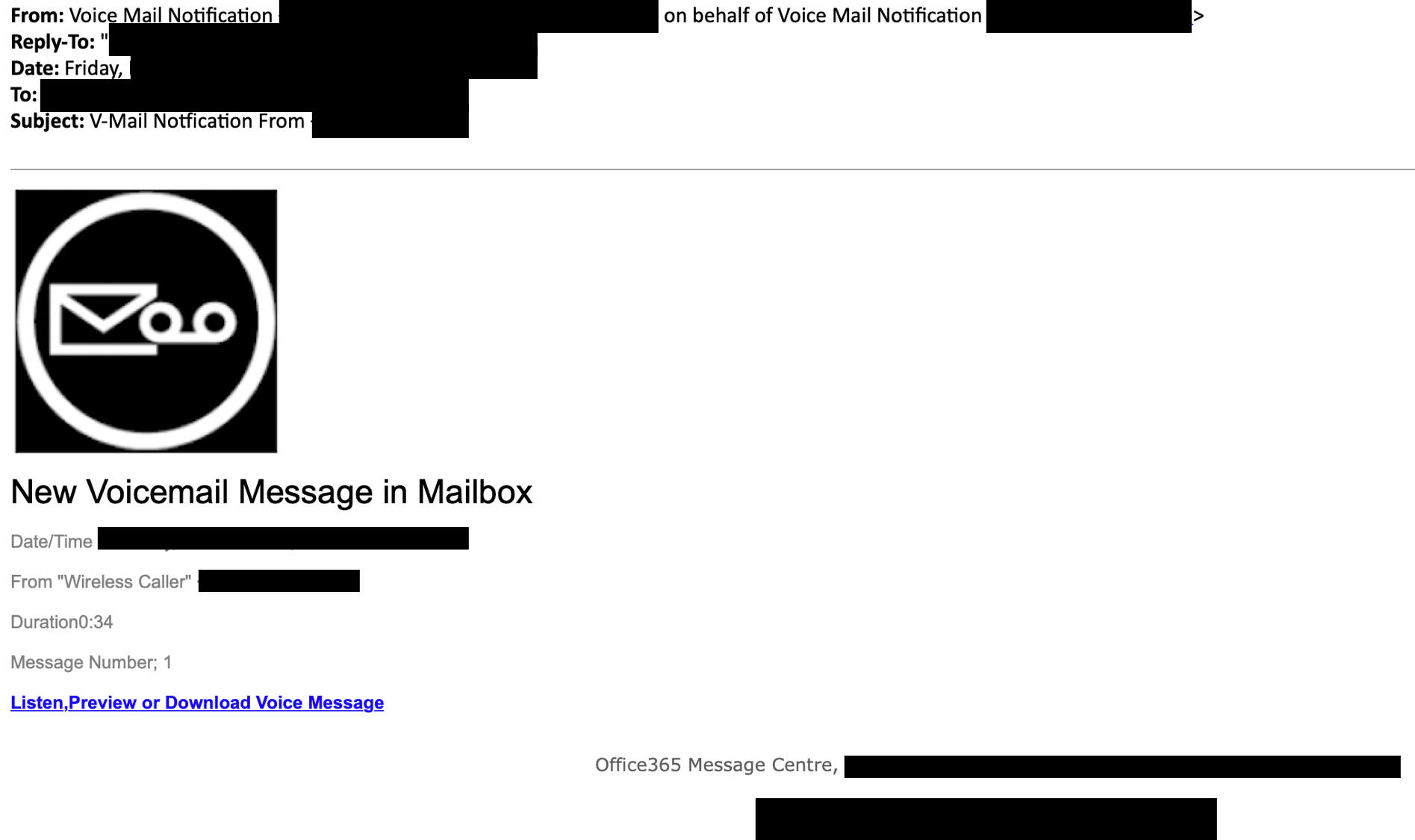
The “From” field:
“Voice Message Notification (“sender” email address) on behalf of Voice Mail notification (second “sender” address)”
The subject:
V-mail notification from (specific phone number)
The body of the message:
“New Voicemail Message in MailboxFrom: Wireless Caller (phone number)
Duration: 0:34
Message Number: 1”
The call to action:
“Listen/preview or Download Voice message.”
The goal:
Attackers are attempting to convince recipients to download the voicemail file containing malicious content by suggesting that the user click the link to preview the message.
Looking ahead to 2020
Since these attack campaigns are low effort for cybercriminals to automate, voicemail phishing attacks will continue to grow in frequency and complexity over the next year. Microsoft Office 365 will continue to be a repeated target of this type of occurrence as the user base is immense.
It’s no secret that phishing attacks can be enormously costly (in the billions of dollars) and destructive, and new scams are appearing every week. GreatHorn finds that 33.9% of white-collar professionals report credential theft attempts bypassing their email security tools, while 32% see business services spoofing attempts in their inboxes.
GreatHorn recently announced new capabilities to proactively identify and block Office 365 credential theft attempts using computer vision. If you would like to learn more, please read our press release or blog.




