For most organizations, this week marks the fourth week of widespread and nearly universal work-from-home policies in response to the global COVID-19 pandemic. And yet despite the time that’s lapsed, for many workers, there’s still no sense of a “new normal” – between juggling child or elder care, homeschooling, mental and emotional fatigue, and physical isolation, it’s safe to assume that very few of your employees are at the top of their game with their day jobs – let alone recalling that security awareness training you did months ago.
Cyber Criminals Are Out In Force
But of course, cyber criminals are NOT taking a break – from Zoom bombing to website attacks – hackers are finding many ways to wreak additional havoc. In fact, GreatHorn data shows that total email-borne threats increased by 77% from February to March, and that COVID-19 email threats increased by more than 6x.
The combination of this increased volume of attacks with a significantly distracted employee base may seem unique to our current situation, but the truth is that the combination of factors is present even in the best of times – albeit not on a global scale. Yes, COVID-19 threats have increased our risk surface – but it’s also exposed inherent weaknesses in how the industry protects against email threats. There will always be a distracted employee and a clever threat that bypasses a blocking defense.
Moreover, this great experiment of remote work is likely to permanently shift the balance of office presence. Organizations previously resistant to remote workers have been forced to figure out ways to adapt, and even after this crisis has passed, many will be more open and tolerant of remote workers than they were before. Forbes recently reported that 75% of CFOs “plan to move at least 5% of their workforce that had previously reported to an office to a full-time, remote schedule.” So remote working is here to stay.
Combat Greater Phishing Risk with User-Focused Tools
Regardless of how long this enforced remote work environment lasts (or what long-term effects it might have on how we work), we can use this as an opportunity to rethink how to better protect employees from email-borne threats.
To better protect yourself there are two fundamental assumptions that we need to accept:
- There will always be some email threat that your first layer of defense does not catch (and in fact having too tight calibration can be detrimental to business velocity)
- Some percentage of your employees will not remember to employ your training when it matters most.
At Hersha Hospitality Management, they’re used to working with employees that aren’t information security savvy, so over the years, they’ve created a simple warning system for such employees to protect themselves from email threats. Says Jason Shane, VP of Technology at Hersha Hospitality Management, “We’ve found that our employees are far more likely to follow those best practices when we provide proactive tools that remind them at the moment of risk.”
That’s where in-the-moment education comes in. Here at GreatHorn, this can consist of a number of different components.
Make Remote Workers Your Front Line of Email Defense
GreatHorn Reporter – a simple and easy Outlook plug-in and a Chrome plug-in for GSuite that provides users two critical pieces of functionality:
- A way to quickly and easily report a phishing threat to the security team with its “Report Phish” functionality
- Clear, digestible indicators as to the relative threat of any given email.
In GreatHorn, user phish reporting is directly tied in to the administrative console, making it simple and easy for the security team to evaluate the threats reported by the end users, identify the breadth of the attack across all mailboxes, and quickly remove them from harm’s way.
GreatHorn Reporter also provides employees with clear stop-light level visibility into the risk level of an email. Instead of telling employees to review header information (which, no matter how excellent your training, many employees will neither review nor understand), they can see 5 critical pieces of information:
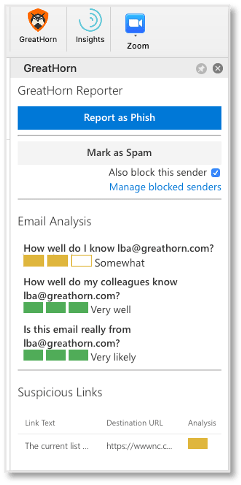
- The sender’s email address (particularly helpful on mobile devices where such information is often obscured)
- The degree of bidirectional communication between the sender and the recipient (“How well do I know [email address]?”)
- The degree of bidirectional communication between the sender and other people in the company (“How well do my colleagues know [email address]?”)
- The likelihood the email is being spoofed (“Is this email really from [email address]?”)
- Any suspicious links in the email
With this information clearly laid out, users are able to make better decisions about whether to interact with email.
Since GreatHorn Reporter can be universally deployed without disruption or even employee involvement, it can be quickly and easily rolled out to employees.
Use Clear, Targeted Banners to Warn Employees of Threat
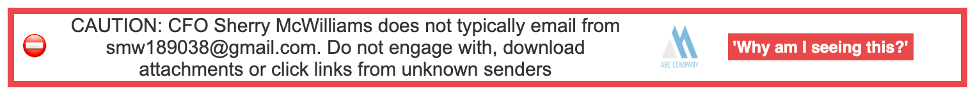
GreatHorn Reporter is often most effective when paired with GreatHorn banners. Busy and distracted employees can easily miss the subtle clues that indicate a threat – particularly when on a mobile device. With the use of email banners, you can clearly indicate to employees why an email is risky and what they should do about it.
A New Era of User Education
Tools like those outlined above are not intended to be a replacement for your security awareness program. However, by providing clear and specific warnings to employees in the moment they are most at risk, security professionals can significantly reduce and even eliminate employee engagement with potential threats.
GreatHorn customer Jeff Kohrman, formerly the global security leader at HashiCorp, explains it this way:
“We ended up building our security awareness training program around the core components that GreatHorn provides like proactive alerts and the ability to build out those alerts to educate people with every email. With GreatHorn, everyone understands their role, their responsibility, and the level of risk associated with each email message.”
These banners can highlight a wide variety of risks from a more obviously dangerous email that purports to be from an executive but is actually coming from an unknown Gmail account, to a potentially legitimate invoice from an email address that the company has never seen before. Whether legitimate or not, such emails warrant additional scrutiny by the recipient to confirm their validity and protect the company from potential harm.In addition to warnings of potential threats, banners can also be used to reinforce business processes that have been disrupted by the new working reality – more on this in a future blog.
For more on changing the mindset of security awareness training, read our previous post on the subject, Flipping the Script on Security Awareness Training.






