On April 11, GreatHorn’s threat response team identified a widespread credential theft attack. Phishing attacks commonly exploit trusted brands by using look-alike domains, display name spoofing, and other social engineering techniques to mask their intent and lend credibility to their attempts. In addition to spoofing Microsoft’s brand in the display name, the attackers spoofed the return path and received headers of a well-known email security company. The attackers crafted the received headers so that it appears to have gone through multiple “Barracuda” hops prior to sending the email via a server designed to look like a Barracuda server. Microsoft has then automatically appended legitimate received header details to the spoofed headers, making it appear that much more legitimate.
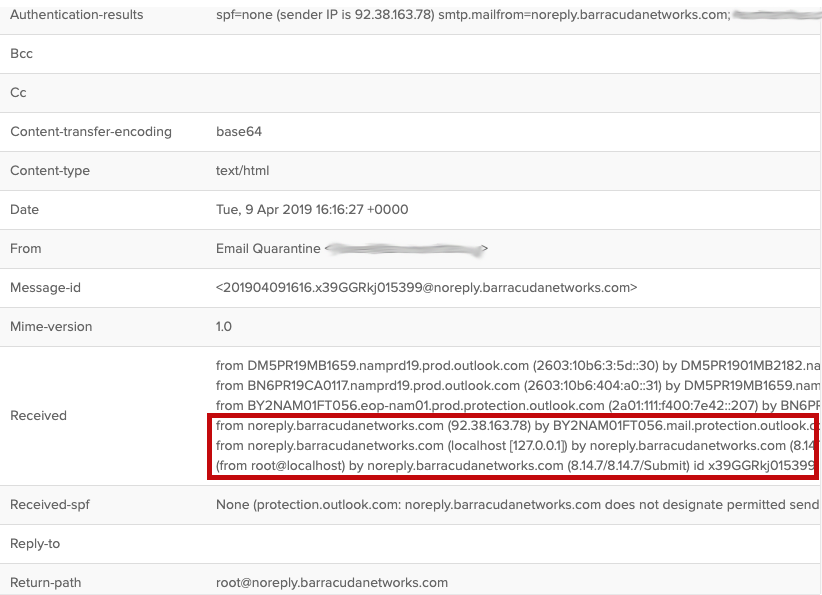
Header data has been well-crafted to spoof a well-known email security company’s domain
The attack exploits a well-known security flaw in Google and Microsoft’s handling of authentication frameworks such as DMARC. While an organization can dictate how it wants DMARC failures and exceptions to be handled, Microsoft Office 365 typically ignores those directives and, at best, treats them as spam or junk instead of quarantining or rejecting them, making it more likely for the user to interact with such spoofs. (Stay tuned for a more in-depth blog on this topic.)
To the recipient reviewing header data then, the technical received header data now appears that much more legitimate – perhaps even validated by Barracuda (though it obviously has not been). This attack shows a much higher degree of sophistication than we typically see in credential theft attacks and is designed to not only fool the unsuspecting, but also to circumvent user-awareness training that teaches users to review header data before interacting with an email.
While the spoofing victim in this case was Barracuda, you could easily see this strategy replicated using any other well-known security company to try and trick more savvy users.
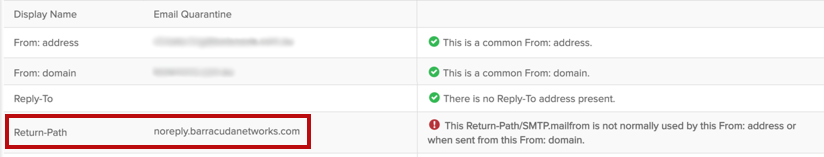
The attackers make it appear that the email is coming from a legitimate barracudanetworks.com return path.
Designed to steal Office 365 credentials, the attack spoofs one of several Microsoft alert types around Quarantine, SharePoint, and OneDrive. The sending email address is a direct spoof of the recipient, e.g. if the victim’s email address is [email protected], the sender email address would also be [email protected].
The attack that reached nearly a quarter of GreatHorn’s customers across many industries and company sizes was seen in both Office 365 and G Suite environments, and bypassed native Office 365 protections in many instances.
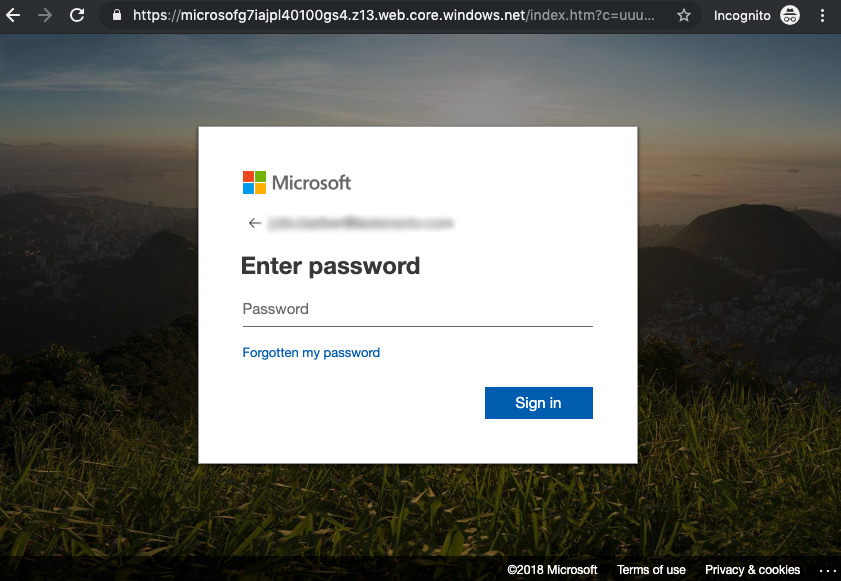
Embedded email links are directed to a pre-populated Microsoft Office credential theft page
The emails themselves follow a relatively standard formula for volumetric credential theft attacks, using light customization, subject-specific display names and subject lines, and a credential theft website that pre-populates the victim’s email address.
As of 8:00am (ET) on April 12th, a subset of the attack links were still active.
| Display Name | Return Path | Subject Line |
| Email Quarantine | noreply.barracudanetworks.com | Message Notification: You have 6 new emails |
| Microsoft OneDrive | noreply.barracudanetworks.com | Your OneDrive is out of storage space |
| [email protected] | clever-barracuda.rmq.cloudpro.com | File “Bonus Account Form.xls” Has Been Uploaded to Onedrive” |
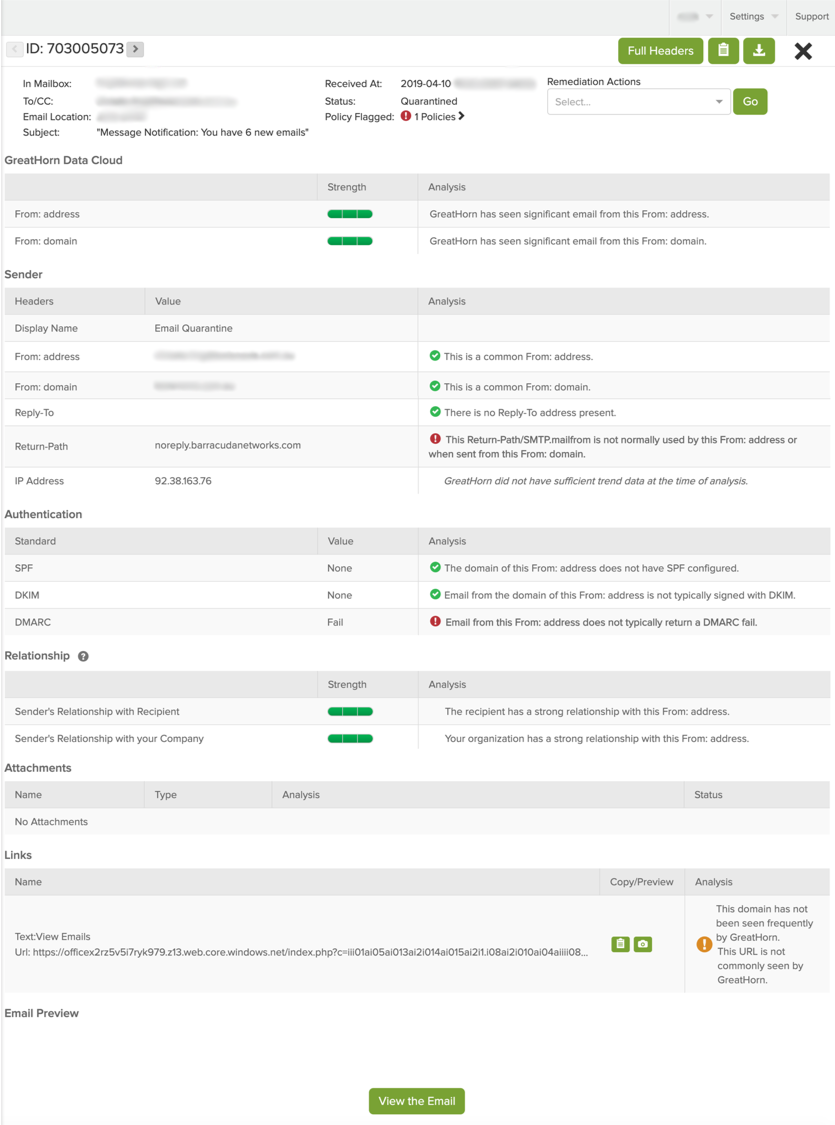
GreatHorn analysis screen of one of the identified emails
GreatHorn Email Security Response
- The malicious emails were flagged under GreatHorn’s impersonation policies.
- The links were correctly identified as suspicious under GreatHorn’s adaptive detection techniques.
- All attack emails in GreatHorn’s customer base have been removed from both customer inboxes and junk folders, regardless of the actions associated with the original policy.
- All customers of GreatHorn Email Security can rest assured that this destination has been added to GreatHorn’s blacklist, ensuring that all future emails will be blocked.
- This weekend, as part of a previously planned initiative, GreatHorn will enable a number of new policies designed to identify an even broader set of brand impersonations and business service spoofing attacks (similar to these). Customers should review these policies and enable the appropriate actions commensurate with their risk tolerance.





