This is the second in our five-part series evaluating anti-phishing tools. To start at the beginning, read our last blog post, “Automated phishing response tools: 4 things to consider” In the last blog in our Automated Phishing Response series, we highlighted four critical considerations for evaluating anti-phishing tools.
Advanced email threat detection ISN’T the (only) answer
In this post, we focus on the most overlooked capability – threat remediation – and its role as your last line of defense.
Of course, the goal is always to remove phish before users can interact with them. Most email security tools are single-mindedly focused on advanced threat detection with the rather unrealistic promise of blocking all threats before they reach users. Certainly, it’s true that sophisticated and polymorphic detection is the first layer of defense to any email security platform.However, these tools often fail to provide robust capabilities for managing and removing the risk of any email threats that make it through that first layer of detection—this limits security teams’ ability to catch attacks before they cause damage.
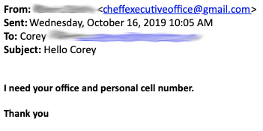
Consider, for example, a targeted phishing attack that mimics an existing vendor but requests a “new method of payment” because of COVID-19 disruptions or an impersonation of an executive using a personal Gmail account – both such attacks frequently bypass legacy email security tools, leaving your organization at risk.
The truth is, no matter how “sophisticated”, “intelligent”, or “advanced” your email threat detection, there will always be a phishing attack that will make it to your end user.
Phishing Remediation Scripting: Manual, Time-Consuming, and Imprecise
Most companies we talk to already know that 100% email threat detection and blocking is an unattainable goal. Their incident response and SOC teams are set up for phishing response, and they may even have a SIEM playbook for phishing.
The challenge is that without robust phishing response tools that can remove email threats from your environment, your team has to rely on scripts to find and remove such threats. This process is both opaque and imprecise – lacking the visibility and assurance that response teams need to be sure they a) have identified every threat (particularly difficult for polymorphic attacks), b) haven’t also removed regular emails by accident, and c) act FAST to minimize exposure.
The CISO of one multi-billion-dollar international company explained their process before GreatHorn this way:
“We had to write a custom script that went through the entire O365 tenant looking for those emails to delete – it took us days. The only time we went through the effort was when we had truly malicious code. Otherwise, we’d just block the link and hope that would be enough.”
Architectural Disadvantages Hamper SEG Remediation
Increasingly, we’re seeing both traditional email security and newer API-based anti-phishing tools tout remediation capabilities. But what many of them don’t reveal is that such threat removal capabilities are often very limited and surprisingly manual.
Even today, very few email security vendors provide any email threat remediation tools at all. The tools that have some form of remediation are often rudimentary at best, failing to incorporate capabilities that should be standard. Here’s a list of things to consider when evaluating incident response:
- Bulk remediation / remediation at scale: How does the tool handle a volumetric attack that’s hit a high percentage of your company? How quickly can it remove hundreds or thousands of attacks from your user mailboxes?
- Robust search for polymorphic attacks: What parameters can you use to search for threats? Are you limited to a small number of parameters such as email address, subject line, URL, and file hash, or can you use other parameters such as header data, IP addresses, and return paths? Can you perform multi-vector searches and exclusions?
- “Find similar”: When you’ve identified an emerging volumetric threat in your environment, is there a simple and easy way to find all emails that are part of that attack?
- Review results prior to deletion: How easily is it to review (and remove!) results before deletion? What happens when a search is too broad and catches legitimate email?
- Phish report integration: Is email removal integrated with user phish reports for quick review and “search for similar” removals?
- Integration with other security tools: Is there a way to integrate removal capabilities into other security tools like a SOAR platform?
- Single-pane of glass visibility: For organizations with multiple domains, can you conduct remediation across all domains in your organization or do you need to do it one domain at a time?
The inherent architecture and workflow of legacy Secure Email Gateways result in detection and response times that are still too long, exposing the company to risks that could be mitigated. New threats remain hard to find and hard to detect. Simplistic searches with limited options make it difficult to understand the scope of polymorphic attacks. Workflows that require switching between multiple modules and capabilities that limit response teams to single-message or small-batch deletion lengthen threat removal time.
These deficiencies exist because secure email gateways, cloud email platforms, and even newer anti-phishing add-ons were architected not around supporting the comprehensive email security lifecycle but rather on the historical detect/block model best suited for the malware-heavy threat landscape of 20 years ago.
Complete Phishing Remediation in Five Minutes or Less
Companies no longer need to settle for rudimentary and manual incident response. Built on a belief that effective email security requires equal attention to protection before, during, and after an attack, GreatHorn’s email security platform includes integrated and comprehensive threat remediation tools for effective incident response against phishing attacks.
GreatHorn supports threat remediation in many different forms:
- Automated removal – Threats are analyzed upon ingest against your company’s risk tolerance and profile and are automatically removed accordingly. In addition, as GreatHorn identifies fast-moving or zero-day threats moving throughout multiple clients, we’ll deploy a universal policy to automatically remove those threats from your environment.
- Suspicious email confirmed as malicious – GreatHorn’s in-the-moment education will warn employees of emails deemed as suspicious but aren’t quarantined based on your company’s risk tolerance. Administrators can investigate such suspicious emails in the dashboard, confirm malicious intent, and bulk remove them from user mailboxes, even after delivery.
- User phish reports – Customers using GreatHorn’s mail plug-in, GreatHorn Reporter, may have phish reports to review. As their employees report phish, not only does that email get immediately removed from the user’s inbox, security teams have the ability to review and “search for similar” to easily bulk remove from other employees’ mailboxes as well.
- Manual search – Sometimes security teams need to conduct a search outside of an obvious triggering event. In this case, GreatHorn’s robust search and forensics capabilities provide the visibility they need, enabling search across dozens of parameters including links and file hashes, display names, sender emails, header data, subject line, and more. This makes it easy to find polymorphic threats that change as they move through your environment.
More Than Just Threat Removal
In addition to bulk deletion, GreatHorn’s incident response capabilities also provide full-click tracking for suspicious URLs to help you isolate users that engaged with the threat prior to removal and target them for further incident response. You’ll be able to determine not only who received a particular email, but also whether they clicked through to the destination and at what time.
In the next post in our anti-phishing evaluation series, we’ll discuss user engagement tools – what they are and why they matter – as well as the importance of incorporating in-the-moment training into your phishing response plan.





